Comprehensive IT monitoring is essential, as IT plays a central role in the value chain for companies.
What to Expect Here – An Overview
2. Which components should be monitored?
3. Why is IT monitoring important? What are its advantages?
4. What is the difference between external and internal IT monitoring?
5. How do I find the right thresholds?
6. What functions does IT monitoring software have?
7. How does a typical monitoring process with a customer work?
What is IT monitoring?
IT monitoring involves the ongoing monitoring of operations and processes in the relevant system environment to ensure their functionality. The overarching goal is to ensure the smooth operation of the IT infrastructure. To achieve this, problems and their causes must be prevented. If a problem does occur, it must be identified at an early stage and resolved as quickly as possible.
IT monitoring checks whether all performance components to be monitored are within the previously defined thresholds. Systematic recording of the results and regular logging enable the data to be analyzed, future trends to be identified, and decision-making impulses to be derived.
Which components should be monitored?
IT monitoring allows dedicated monitoring of a company's IT infrastructure, whether for hardware or software. It is particularly important to integrate all relevant components into a comprehensive solution, as this is the only way to ensure seamless monitoring and smooth operation. This means that, in addition to resources such as storage capacity or RAM utilization, applications, processes, interfaces, directories, and logs can also be monitored. In principle, all components can be monitored and read.
Why is IT monitoring important? What are its advantages?
Comprehensive IT monitoring offers several advantages in addition to higher IT availability and stability.
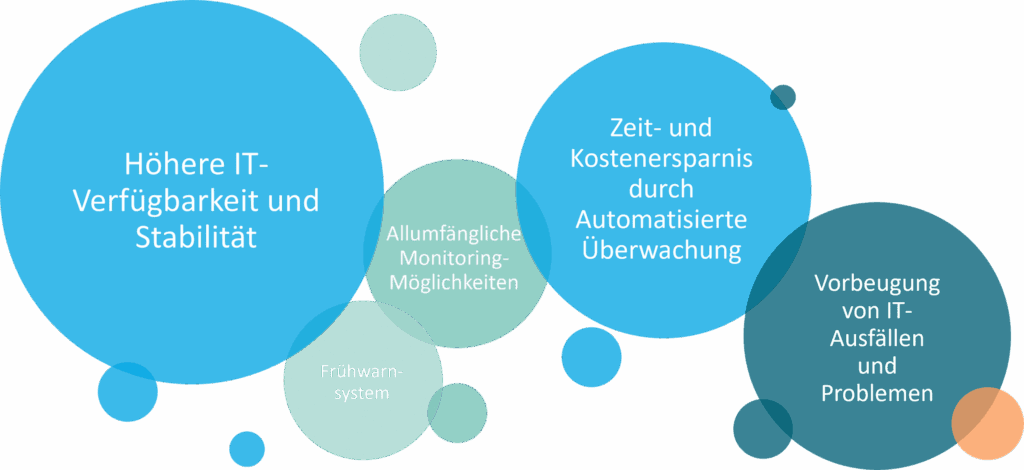
Figure 1:Advantages of IT monitoring | isr.de
Active IT monitoring replaces manual infrastructure checks with automated monitoring. This saves time and money. Companies can use this saved time to focus on business-critical processes.
IT monitoring also helps prevent a worst-case scenario for companies: the failure of IT and thus important operational functions. The notification function, which is triggered when defined thresholds are exceeded or approached, ensures early detection of malfunctions and problems. This early warning system makes it possible to prevent problems before they even arise and to troubleshoot them as quickly as possible. This ensures the continuous operation of the systems.
In addition to the familiar server, network, storage, database, and environment monitoring, certificates, version statuses, and sufficient software licensing can also be comprehensively monitored. Application monitoring is particularly important, as this is currently still very rudimentary or carried out manually. Proactive action in IT often replaces the current practice of responding to fault reports from users.
What is the difference between external and internal monitoring?
Internal monitoring means that companies regulate the monitoring of their systems completely independently using structures they have implemented themselves on the components to be monitored. However, internal monitoring carries the risk of being affected by malfunctions that spread throughout the entire infrastructure, including monitoring, and therefore remain undetected.
In contrast, with external monitoring, a company must act as a Managed ServicesWhat are managed services? Managed services can be defined as IT services... More (e.g., with ISR) does not have to worry about tool provisioning or licensing. The major advantage is end-to-end monitoring of applications and IT infrastructure based on best practices. Intelligent and comprehensive monitoring is performed, particularly for applications.
How do I find the right thresholds?
It is clear that the correct definition of individual thresholds is of great importance for IT monitoring. Only with the right thresholds can problems and critical conditions be detected in good time. Based on years of experience in IT monitoring, ISR has therefore developed the following procedure for determining thresholds:
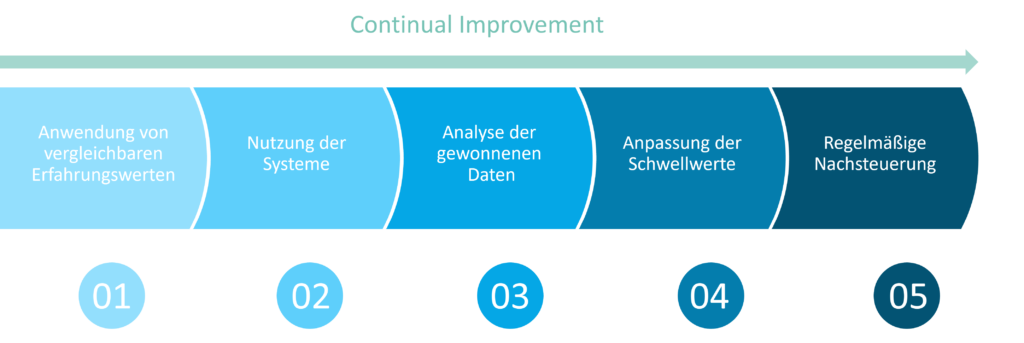
Figure 2:Process for determining threshold values in IT monitoring | isr.de
In a first step, empirical values from the past are applied to comparable systems and constellations. The systems are then used with these empirical values over a certain period of time. The data obtained through use is then analyzed and the threshold values adjusted accordingly. This is followed by regular adjustments, for example when incidents occur. This ongoing process is also known as continual optimization. In this way, monitoring is continuously improved, adapted to the unique characteristics of the specific IT infrastructure, and enables problems to be detected as accurately and early as possible.
What functions does IT monitoring software have?
The corresponding monitoring software is installed on the server to be monitored and enables the encryption, transmission, reading, and evaluation of the data.
There are several IT monitoring software programs available. Which software is best suited to an individual company depends on various factors, such as the specific requirements of the individual infrastructure, the preferred type of monitoring, and the desired notification function. In addition, despite regular and comprehensive checks, the software should not place any additional strain on the system.
At ISR, we use Checkmk from tribe29 GmbH as monitoring software for our customers because Checkmk offers a high degree of flexibility in adapting to individual customer monitoring requirements and provides increased security and reliability.
How does a typical monitoring process with a customer work?
IT monitoring is a process that requires adaptation to the specific characteristics of each infrastructure. We have developed a best practices approach for standard cases, which nevertheless allows for individual adjustments at any time:
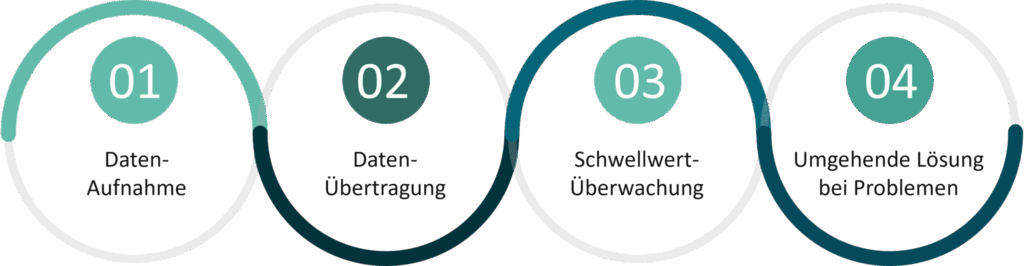
Figure 3: IT monitoring process at the customer's site | isr.de
01 Readingdata at the customer's premises and encrypting readable files
02 Transfer of data to our monitoring servers using a secure process (via sFTP or FTPs) for data evaluation
03 If a threshold value is exceeded: immediate notification to us via instant messaging (e.g., Microsoft Teams)
04 Immediate solution development by one of our experts before our customer even notices that there is a problem
This process enables the systems to operate smoothly.
Do you have any questions? Feel free to contact us!
Professional IT monitoring is therefore an important security aspect for your company's IT and is crucial for the reliable operation of your systems. If you are interested in further information on the topic of IT monitoring or are wondering how you can implement monitoring in your company, please feel free to contact us or visit our Application Management page.

Jens Brettschneider
Head of Business Unit
Application Management
jens.brettschneider@isr.de
+49(0)151 422 05 425


